DeRISK CRQ (Cyber Risk Quantification)
OT stakeholders, CISOs, CFOs, site managers, and boards need financially quantified cyber risk insights to optimize industrialcybersecurity investments and demonstrate cyber risk governance.

DeNexus’ DeRISK Platform
DeRISK™ is the only evidence-based, data-driven platform that translates OT cyber risk exposures and vulnerabilities into financial metrics — Value at Risk (VaR) and Estimated Financial Loss — so executives and boards understand the business impact of potential cyber incidents across their industrial portfolio.
Financial risk metrics feed directly into risk mitigation simulations, enabling industrial organizations to prioritize cybersecurity investment and optimize security controls for maximum risk reduction.

DeRISK empowers executives to make better cyber risk management decisions
DeRISK sets a new standard in industrial cyber risk management. The only solution that quantifies OT cyber risk using both inside-out asset and vulnerability data and outside-in threat intelligence, with sector-specific probabilistic modeling. Executives and boards make reliably informed, financially grounded decisions about cyber risk governance — aligned with NIST CSF, ISO 27001, and the DeNexus DNX CSF framework. See How >
Key Capabilities
Dynamic Risk Aggregation
Site and portfolio-level OT cyber risk analysis combining inside-out asset and vulnerability telemetry with external threat intelligence and firmographic outside-in data.
Attack-Path Mapping
Dynamic mapping of potential OT attack paths and loss events — leveraging MITRE ATT&CK; for Enterprise and MITRE ATT&CK; for ICS — with hundreds of actionable attack graphs for industrial environments.
Quantification of Risks
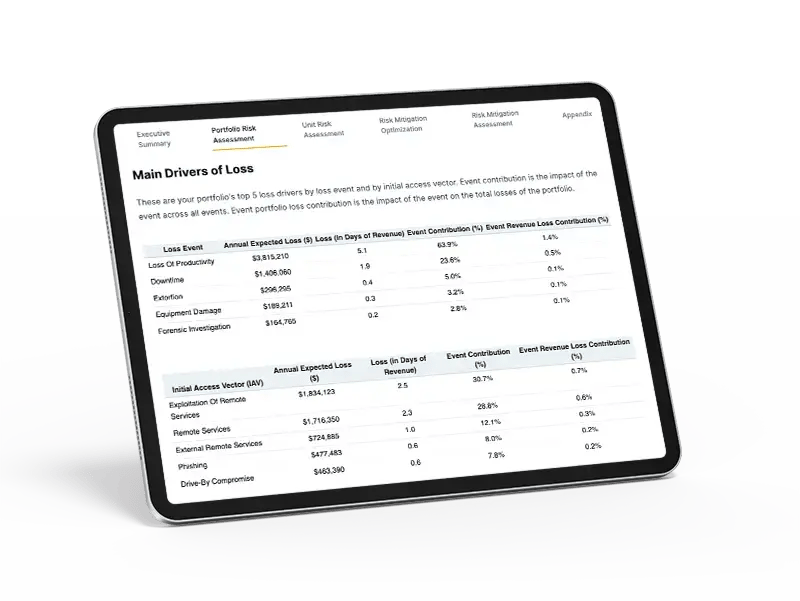
Financial risk metrics including Value at Risk (VaR) and Estimated Financial Loss, top drivers of OT cyber risk, loss event types, and industrial facilities ranked by financial risk contribution.
Risk Mitigation Simulation
What-if OT cyber risk reduction simulations to prioritize risk mitigation actions and optimize security control investments across industrial sites and portfolios.
Industry Peer Benchmarking
Sector-specific peer benchmarking of OT cyber risk posture — across manufacturing, energy, data centers, and utilities — at site and portfolio levels.
Audit and Compliance
OT cyber risk posture evaluation mapped to NIST CSF, ISO 27001, or the DeNexus DNX CSF framework — supporting NIS2, NERC CIP, and DORA compliance readiness.
Executive Reporting
On-demand, board-ready reports delivering financially quantified OT cyber risk metrics for executive review, cyber risk governance, and insurer disclosure.
DeRISK Run-Through
DeRISK combines internal OT telemetry — assets, vulnerabilities, and security controls — with external threat intelligence and firmographic data to assess threat-actor attractiveness, identify the most likely industrial attack paths, and quantify the financial impact of potential cyber incidents through a probabilistic digital-twin simulation engine.
Request DemoElevating Cyber Risk to the Boardroom
DeRISK transforms cybersecurity telemetry into financial risk metrics shareable through executive reports available on-demand to bridge the gap between the control room and the boardroom.
Identify Cyber Threat Sources
By aggregating granular OT security signals from disparate tools and mapping them to MITRE ATT&CK; for ICS and Enterprise, NIST CSF, and ISO 27001, DeRISK identifies the origin and trajectory of your industrial cyber risk — so you target mitigation actions with precision and demonstrate control improvement over time.
Quantify Risks in Monetary Terms
OT cyber risk quantified in financial terms — Value at Risk (VaR) and Estimated Financial Loss — guides executive investment decisions, tracks risk
Know the business impact of cyber risk.
Know where to start with risk management.
0
data sources
0
billion simulation runs weekly per site
0
pre-configured risk mitigation strategies
Solve Cyber Risk
Request a demo of the world’s first cyber risk quantification and management platform.
Request A Demo